Core Switch Security Hardening Design Guide
A comprehensive, implementable security baseline for core switches deployed in data centers, campus networks, and mission-critical business environments. Covers management plane, control plane, and data plane hardening with full operational guidance.
System Overview
This Core Switch Security Hardening Design Guide defines an implementable security baseline for core switches deployed in data centers, campus networks, and mission-critical business networks. The objective is to reduce risks of unauthorized access, malicious or accidental configuration tampering, control-plane attacks (CPU exhaustion, protocol abuse), excessive management exposure, and L2/L3 protocol misuse that can lead to outage—without compromising high availability or forwarding performance.
The scope of this guide encompasses management plane, control plane, and data plane hardening for core switches and their immediate dependencies, including jump hosts, AAA servers, logging infrastructure, time synchronization, configuration backup, and the management network. Out of scope are endpoint security, application security, DLP, and non-switching appliances unless they integrate for logging or AAA purposes.
Key inputs required for implementation include: network topology, routing protocols in use, HA design (stack/MLAG/chassis redundancy), current switch OS versions, existing AAA/logging/NTP infrastructure, and operational constraints. Deliverables include procurement-ready requirements, implementation steps, acceptance tests, and an operational baseline checklist with vendor-neutral commands adaptable to any platform syntax.
The core value of this guide lies in providing a unified, auditable, and performance-safe hardening blueprint that aligns security controls with routing stability and HA behaviors. Key dependencies include: OOB or isolated management VRF, AAA (TACACS+/RADIUS), PKI/SSH key management, Syslog/SIEM, NTP, config backup repository, and change management workflow. The guide covers six typical deliverables: security zoning design, baseline configuration checklist, CoPP/CPP templates, protocol security matrix, acceptance test plan, and O&M runbooks for secure operations.
System Architecture
The overall security architecture is organized into three horizontal planes—Management, Control, and Data—each with distinct responsibilities, trust levels, and protection mechanisms. The diagram below illustrates the complete security domain architecture, showing how each plane interacts and how security controls are applied at every layer.
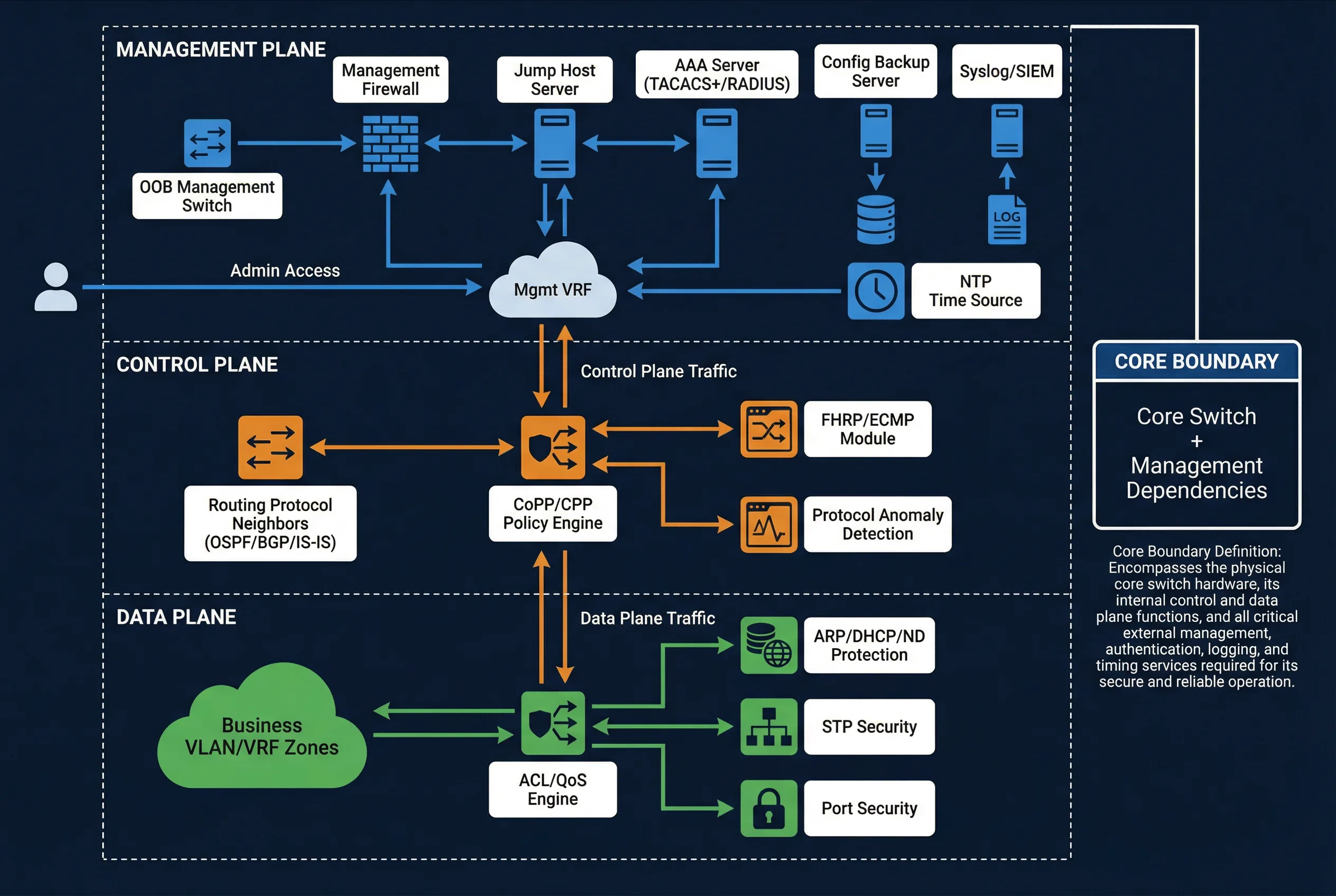
The Management Plane is responsible for identity, access paths, encryption, audit, and configuration lifecycle. All administrative access must flow through a dedicated OOB management network or isolated management VRF, enforced by a management firewall and jump host. The Control Plane handles protocol authentication, rate limiting, CPU protection, and adjacency resilience through CoPP/CPP policies. The Data Plane enforces L2/L3 anti-spoofing, segmentation, minimal exposure, and safe defaults at wire speed.
Major Functions
The hardening baseline is organized around eight functional domains, each following a Design → Implement → Verify lifecycle. Together, these functions provide comprehensive coverage of all attack surfaces relevant to core switch operations, from access path consolidation and identity management to control plane protection and high-availability security consistency.
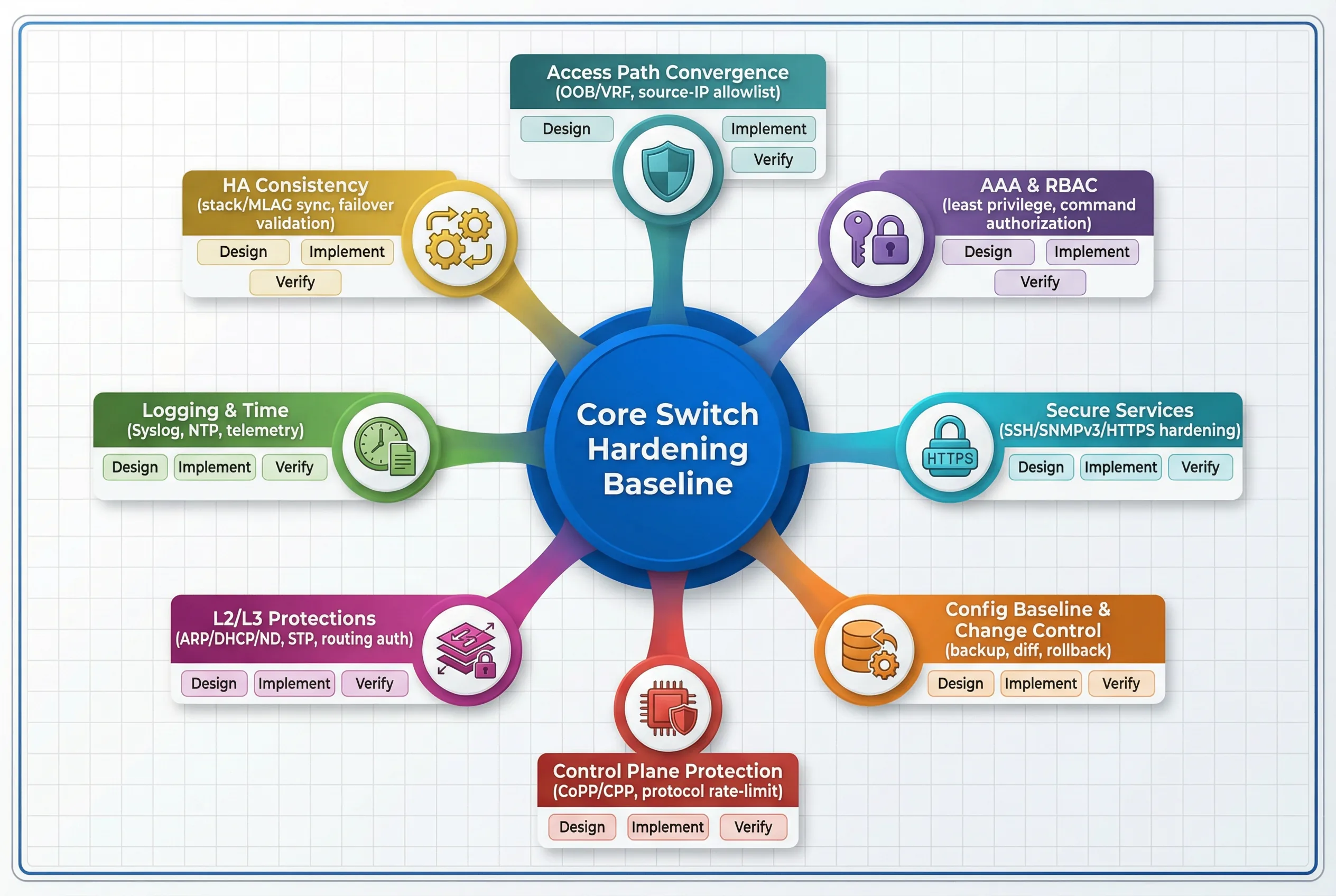
Each functional domain addresses a specific attack surface and operational risk. Access Path Convergence reduces the attack surface by forcing all administrative access through OOB/management VRF and controlled source IPs. AAA & RBAC ensures central authentication and authorization with role separation and command accounting. Secure Services hardens SSH ciphers, enforces SNMPv3, and enables HTTPS with modern TLS while disabling all legacy services. Config Lifecycle Controls provides versioned backups, change approval, automated diff, and rollback capabilities. Control Plane Protection implements CoPP/CPP with protocol-aware policing. L2/L3 Protections covers ARP/DHCP/ND protection, STP security, and routing authentication. Logging, Telemetry, and Time ensures a centralized audit trail with consistent timestamps. HA Security Consistency synchronizes policies across stack/MLAG peers to maintain security posture during failover.
Chapter Navigation
This guide is organized into twelve chapters, each addressing a distinct aspect of core switch security hardening. Navigate to any chapter using the cards below or the left sidebar.
Key Features & Capabilities
Three-Plane Security Model
Comprehensive coverage of management, control, and data planes with distinct protection strategies and acceptance criteria for each layer.
AAA & Zero-Trust Access
TACACS+/RADIUS integration with RBAC, MFA enforcement, command accounting, and break-glass emergency access with full audit trail.
CoPP/CPP Templates
Protocol-aware control plane policing templates that protect CPU from exhaustion while preserving routing adjacency stability under attack conditions.
HA Security Consistency
Security policies synchronized across MLAG/stack peers with validated failover behavior ensuring controls remain intact during switchover events.
Interactive Calculators
Five purpose-built calculators for bandwidth planning, CoPP sizing, availability modeling, log storage, and optical loss budget estimation.
Acceptance Test Plan
Structured acceptance criteria covering functional, performance, stability, reliability, security, and integration test domains with pass/fail criteria.
Scope & Applicability
The following table summarizes the network types, device platforms, and management models covered by this guide, along with the verification approach for each assumption.
| Dimension | Coverage | Verification Method |
|---|---|---|
| Network Types | Data center core (Spine/Leaf or core/aggregation), campus core (collapsed or dual-core), critical business core (WAN/branch hub) | Topology diagrams and routing domain review |
| Core Switch Role | L3 gateway/routing and high-speed aggregation; limited L2 services (VLAN trunking); not treated as access switch | Interface role classification and SVI usage review |
| Device Platforms | Mainstream enterprise/data-center switches supporting VRF, ACL, QoS, telemetry, SSH, SNMPv3, TACACS+/RADIUS, NTP, Syslog, CoPP/CPP | Vendor feature matrix validation |
| Management Model | Dedicated OOB management network preferred; in-band management VRF/VLAN with strict source restrictions as alternative | Mgmt ports/VRF existence and IPAM entries |
| Compliance Targets | Critical-infrastructure and graded protection requirements (MLPS-style controls): auditability, least privilege, secure access, segmentation | Compliance checklist mapping in Chapters 6 & 10 |
| Availability Model | Dual-core/stack/MLAG or chassis redundancy; no single point of failure in management plane reachability for emergency access | Redundancy diagrams and failover test results |