Support & Integration
Chapter 7 — Core Switch Security Hardening Design Guide
Core switch security hardening does not operate in isolation. It depends on a set of supporting infrastructure systems that must be deployed, configured, and integrated before the hardening controls can function effectively. These supporting systems include authentication and authorization servers, time synchronization infrastructure, centralized logging and SIEM platforms, out-of-band management networks, configuration backup systems, and PKI certificate infrastructure. The absence or misconfiguration of any of these systems creates gaps in the hardening architecture that cannot be compensated by controls on the switch itself.
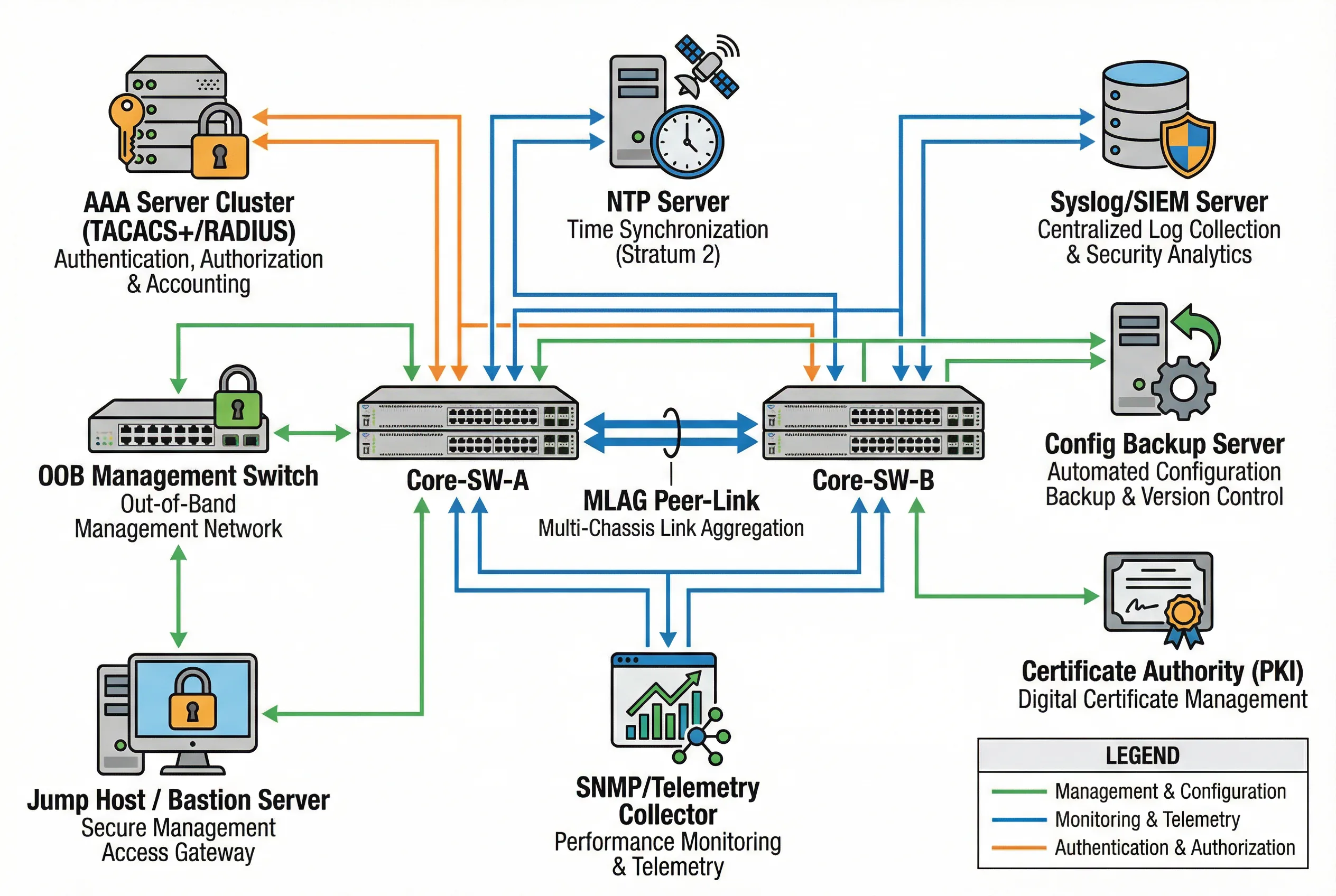
The integrated supporting infrastructure diagram below provides a unified view of all supporting systems and their relationships to the core switches. Each supporting system is connected to the core switches via the OOB management network (green connections), the production monitoring network (blue connections), or the authentication network (orange connections). Understanding these relationships is essential for planning the deployment sequence and ensuring that dependencies are resolved before hardening controls are activated.
7.1 Integrated Supporting Infrastructure Diagram
7.2 Supporting System Requirements
The following table defines the requirements for each supporting system, including the protocols used, redundancy requirements, and the hardening controls that depend on each system. Systems marked as "Critical" must be operational before any hardening controls that depend on them are activated.
| Supporting System | Criticality | Protocol | Redundancy | Dependent Controls | Failure Impact |
|---|---|---|---|---|---|
| AAA Server (TACACS+/RADIUS) | Critical | TACACS+ (TCP 49) or RADIUS (UDP 1812/1813) | Primary + secondary; local fallback account | SSH/console authentication; command authorization; accounting | Management lockout if primary and secondary both fail |
| NTP Server | Critical | NTPv4 (UDP 123); NTPsec preferred | Primary + secondary; GPS-disciplined preferred | Syslog timestamps; certificate validity; RPKI RTR; audit trail | Log correlation failure; certificate validation errors; audit trail unreliable |
| Syslog / SIEM Server | Critical | Syslog over TLS (TCP 6514); RELP for reliable delivery | Primary + secondary; local buffer on switch | Security event logging; audit trail; compliance reporting | Security events lost; compliance audit failure; incident response degraded |
| OOB Management Switch | Critical | Ethernet (management VLAN); physically isolated | Redundant OOB switch; separate power feed | All management access; console server connectivity; emergency access | Loss of management access during production network failure |
| Console Server | High | RS-232 serial; SSH over OOB network | Redundant console server; cellular backup | Emergency console access; password recovery; initial configuration | No console access during network failure; emergency recovery impaired |
| Jump Host / Bastion Server | High | SSH (TCP 22); HTTPS (TCP 443) for web-based access | Primary + secondary jump host; MFA enforced | All SSH/HTTPS management access; session recording; access control | Management access requires direct OOB console; session recording lost |
| Config Backup Server | High | SCP/SFTP over OOB; Git-based version control | Primary + offsite backup; encrypted storage | Configuration version control; rollback capability; change audit | No configuration rollback; change history lost; recovery time increased |
| SNMP / Telemetry Collector | Medium | SNMPv3 (UDP 161/162); gRPC/gNMI (TCP 57400); NetFlow/IPFIX | Collector cluster; local buffer | Performance monitoring; capacity planning; anomaly detection | Performance visibility lost; capacity planning degraded; anomaly detection impaired |
| PKI / Certificate Authority | Medium | SCEP/EST for certificate enrollment; OCSP for validation | Root CA offline; issuing CA redundant | HTTPS management; MACsec certificates; SSH host key verification | Certificate renewal failure; HTTPS management degraded; MACsec key rotation failure |
7.3 AAA Integration Design
The AAA (Authentication, Authorization, and Accounting) system is the most critical supporting infrastructure for core switch security hardening. It provides centralized authentication for all management access, command-level authorization to enforce least-privilege access, and comprehensive accounting of all administrative actions. The design must account for failure scenarios to prevent management lockout while maintaining security during AAA server unavailability.
| AAA Function | Protocol | Configuration Requirement | Failure Behavior |
|---|---|---|---|
| Authentication (Login) | TACACS+ preferred; RADIUS fallback | Primary server + secondary server; local account as last resort | Fall through to secondary; then local emergency account |
| Authentication (Enable/Privilege) | TACACS+ | Separate AAA method list for privilege escalation | Local enable password as fallback |
| Command Authorization | TACACS+ (command authorization) | Per-privilege-level command lists; deny-all default | If AAA unavailable: permit (configurable) or deny all |
| Accounting (Commands) | TACACS+ | All commands logged to TACACS+ server; local buffer | Commands still executed; accounting queued for later delivery |
| Accounting (Sessions) | TACACS+ / RADIUS | Session start/stop logged; idle timeout enforced | Sessions still permitted; accounting queued |
7.4 Monitoring and Telemetry Integration
Effective monitoring integration requires configuring the core switch to export security-relevant events to the SIEM platform in real time. The following table defines the minimum set of events that must be logged and the recommended export method for each event category. Events marked as "Critical" must be exported in real time with no local buffering that could result in event loss.
| Event Category | Criticality | Export Method | Retention | Alert Threshold |
|---|---|---|---|---|
| Authentication failures | Critical | Syslog over TLS; real-time | 12 months | 5 failures in 60 seconds |
| Configuration changes | Critical | Syslog over TLS; real-time; config diff to backup server | 24 months | Any change outside maintenance window |
| BGP session state changes | Critical | Syslog + SNMP trap; real-time | 12 months | Any BGP session down event |
| CoPP drop events | High | SNMP trap + streaming telemetry | 6 months | CoPP drops >1000/min sustained |
| ACL permit/deny hits | High | Syslog (sampled for high-volume ACEs) | 6 months | Deny hits on critical ACEs |
| Interface link state | High | SNMP trap + syslog | 6 months | Any core interface down event |
| CPU/memory utilization | Medium | SNMP polling (5-min interval) + streaming telemetry | 3 months | CPU >80% sustained 5 min; memory >90% |
| Routing table changes | Medium | Streaming telemetry (gNMI); route count monitoring | 3 months | Route count change >10% in 5 minutes |