System Components
Chapter 1 — Core Switch Security Hardening Design Guide
1.1 System Architecture
The core switch security hardening system is composed of multiple interdependent zones, each with a defined trust boundary and set of responsibilities. Understanding the architecture and the relationships between zones is essential before implementing any hardening controls, as misalignment between zones is a common source of both security gaps and operational failures.
The architecture is divided into five primary zones: the Admin Zone (where operators and SOC/NOC personnel work), the Secure Ops Zone (containing jump hosts, bastion servers, AAA, config backup, and PKI), the Network Core Zone (the core switch pair and their upstream/downstream connections), the Out-of-Band Management Network (providing isolated management connectivity), and the Logging & Time Zone (Syslog/SIEM, telemetry collectors, and NTP). All management access must traverse the Secure Ops Zone before reaching the Network Core Zone, ensuring a consistent audit trail and enforcement point.
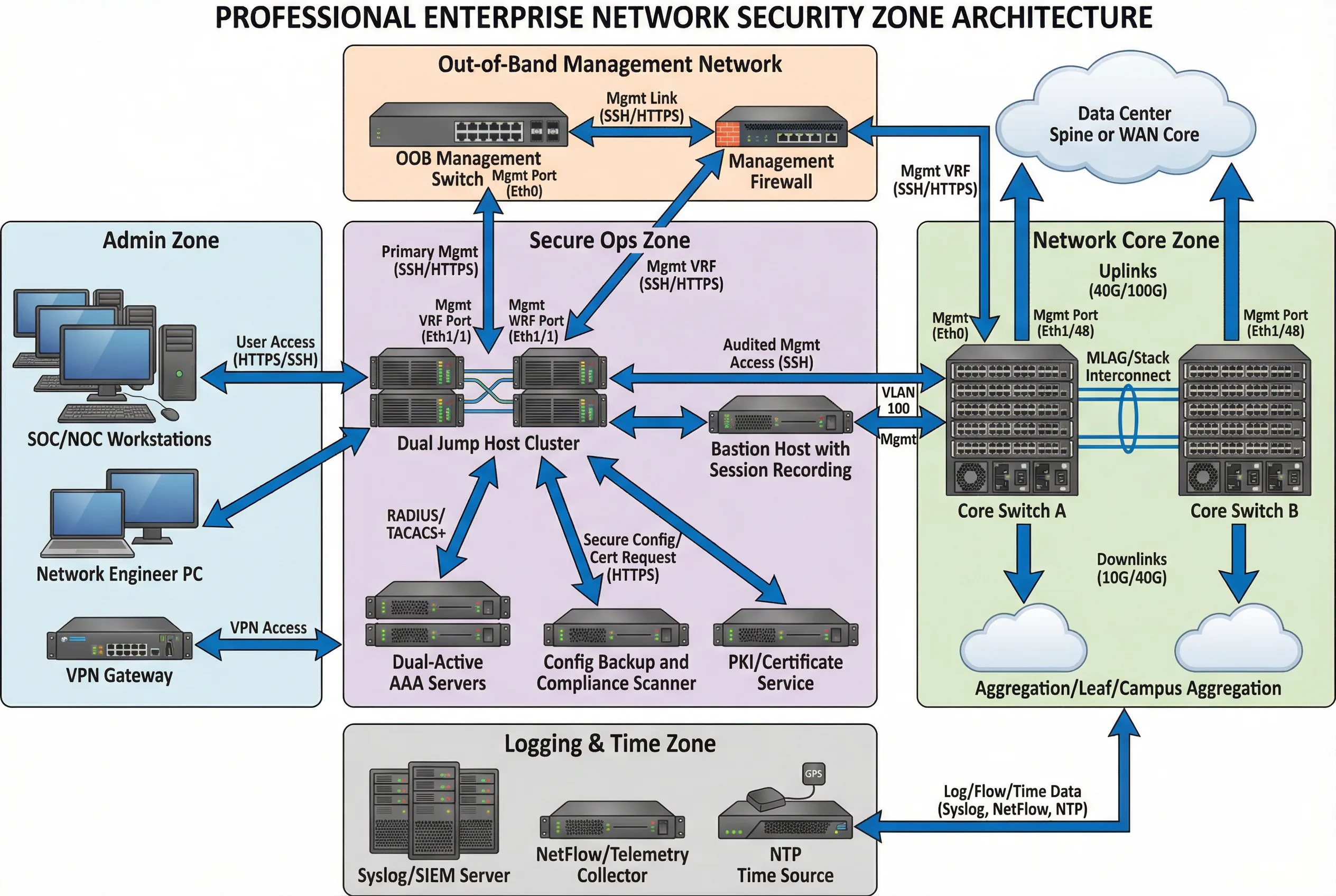
The Out-of-Band Management Network is the most critical dependency for operational resilience. It provides management access even when the production network is degraded or under attack. The OOB network must be physically or logically separate from the production data network, with its own management switch, firewall, and IP addressing plan. All core switch management interfaces (mgmt0, mgmt1, or equivalent) must connect exclusively to the OOB network, never to production VLANs.
Module relationships follow a strict hierarchy: operators authenticate through the Admin Zone, pass through the Secure Ops Zone (jump host + AAA), traverse the management firewall, and reach the core switch management VRF. Logging and telemetry flow outbound from the core switch to the Logging & Time Zone. NTP synchronization flows inbound from the NTP hierarchy to the core switch. Config backups flow outbound to the backup repository in the Secure Ops Zone.
Core vs. Optional Components
Not all components carry equal weight in the hardening baseline. The following classification distinguishes mandatory core components from optional enhancements that improve posture but are not strictly required for baseline compliance.
| Category | Component | Justification |
|---|---|---|
| Core | Management isolation (OOB or mgmt VRF) | Prevents lateral movement from production to management plane |
| Core | AAA (TACACS+/RADIUS) | Required for audit, RBAC, and command accounting |
| Core | Syslog/logging | Required for forensics, compliance, and incident response |
| Core | NTP (restricted) | Required for log correlation and certificate validity |
| Core | Config backup | Required for rollback and change management |
| Core | CoPP/CPP | Required to prevent CPU exhaustion attacks |
| Core | Protocol hardening baseline | Required to prevent routing attacks and L2 spoofing |
| Optional | Automated compliance scanning | Improves posture verification speed and coverage |
| Optional | Streaming telemetry at scale | Improves observability and MTTR |
| Optional | SOAR for automated response | Reduces response time for known attack patterns |
| Optional | PKI automation | Reduces certificate management overhead |
1.2 Components and Functions
Each component in the hardening architecture has specific inputs, outputs, key performance indicators (KPIs), and mismatch risks. Understanding these characteristics is essential for procurement, integration, and ongoing operations. The component card diagram below provides a visual overview of all nine primary components and their operational parameters.
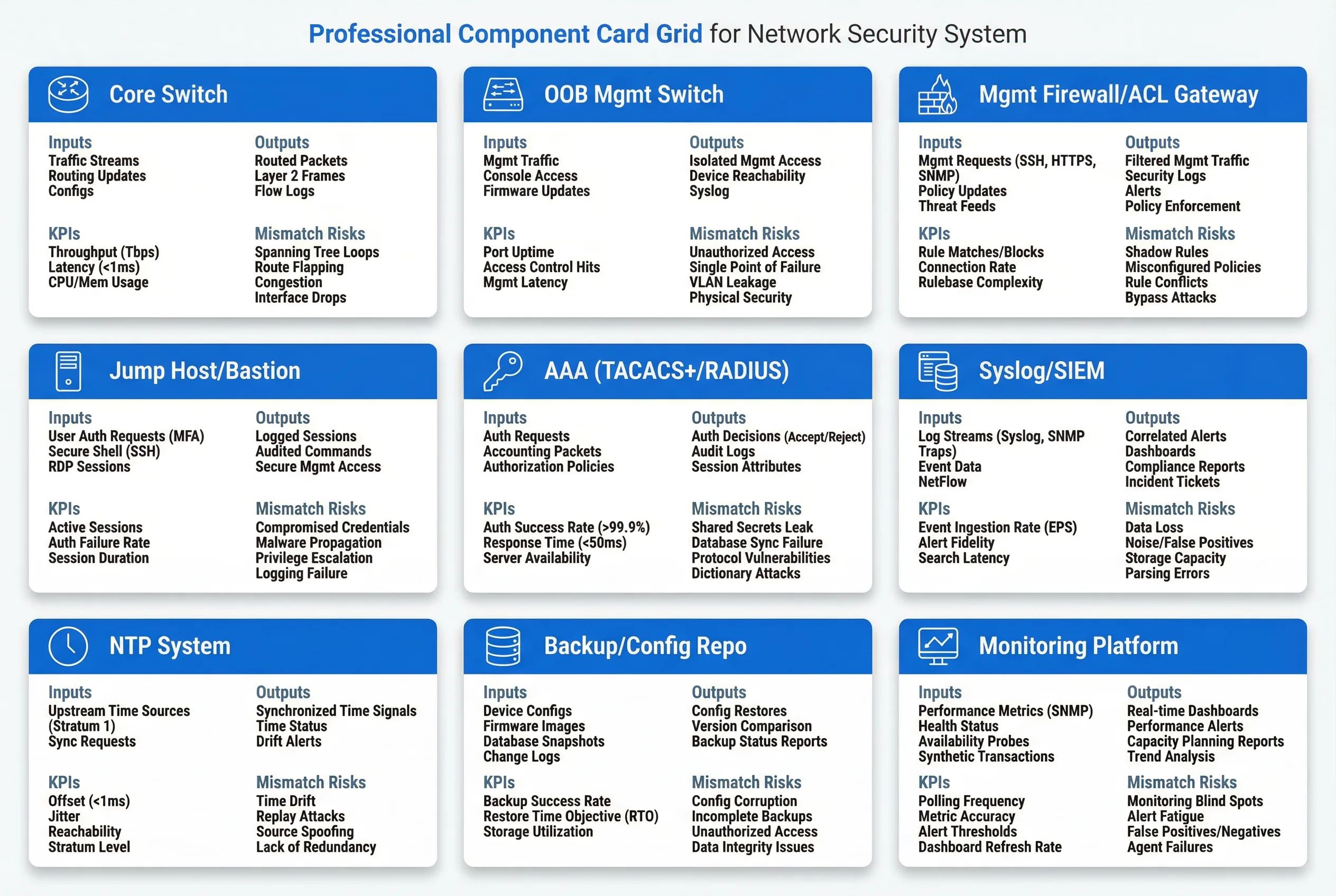
The component checklist below provides detailed specifications for each element of the hardening architecture. Each entry includes the component's primary inputs and outputs, the KPIs used to verify correct operation, and the mismatch risks that arise when the component is misconfigured, undersized, or absent.
| Component | Inputs | Outputs | KPIs | Mismatch Risks |
|---|---|---|---|---|
| Core Switch | Routing adjacencies, management sessions, ACL/CoPP policies | Forwarding, logs, telemetry | CPU <40% steady; control-plane drop counters stable; forwarding loss <design | Insufficient TCAM for ACLs; weak CoPP; limited VRF features |
| OOB Mgmt Switch | Mgmt ports, jump host access | Isolated mgmt connectivity | Mgmt network availability; port security | Unmanaged switch enables MITM; no port isolation |
| Mgmt Firewall/ACL Gateway | Admin VPN/jump host traffic | Enforced allowlist to mgmt IPs | Rule hit-rate; deny log volume | Overly broad permits expose management plane to production traffic |
| Jump Host / Bastion | Operator auth, MFA tokens | Controlled sessions, session recording | Session logging completeness; patch level; MFA enforcement rate | Direct admin access bypasses audit trail; compromised jump host = full access |
| AAA (TACACS+/RADIUS) | Credentials, role assignments | AuthN/AuthZ decisions, command accounting | Availability >99.9%; response latency <50ms; fail-open/close policy | Misconfigured fallback locks out operations or weakens controls; no command audit |
| Syslog/SIEM | Device logs, SNMP traps, alerts | Correlation, retention, compliance reports | Log completeness; timestamp accuracy; ingest latency | Missing logs break audit and compliance; delayed detection of attacks |
| NTP System | Upstream time sources (GPS/stratum-1) | Consistent time to all devices | Drift <100ms typical; stratum policy compliance | Time skew invalidates log correlation; certificate validation failures |
| Backup/Config Repo | Device configurations, OS images | Config restores, version comparison, backup status | Backup success rate; RTO for restore; storage utilization | No rollback capability; config drift undetected; compliance evidence missing |
| Monitoring Platform | Performance metrics (SNMP/telemetry), health status | Real-time dashboards, performance alerts, trend analysis | Polling frequency; alert fidelity; dashboard refresh rate | Monitoring blind spots; alert fatigue from false positives; slow MTTR |
Integration Dependencies
The hardening system components are not independent—they form a dependency chain where failure of one component can cascade to others. The most critical dependency chains are: AAA failure can cause management lockout if fallback policy is misconfigured; NTP failure can cause log correlation failures and certificate validation errors; OOB network failure can leave the core switch unreachable for emergency access; and config backup failure removes the ability to recover from configuration corruption or unauthorized changes.
Deployment Checklist
Before deploying the hardening baseline, verify that all core components are present and operational. The following checklist covers the minimum requirements for a compliant deployment.
- OOB management network is physically or logically separate from production VLANs and has its own IP addressing plan.
- Management firewall rules are configured with deny-all default and explicit allow for jump host source IPs only.
- Jump host cluster (minimum two for HA) is deployed with MFA and session recording enabled.
- AAA servers (minimum two for HA) are reachable from the management VRF with shared secret rotation policy defined.
- Syslog/SIEM is reachable from the core switch management VRF with retention policy configured per compliance requirements.
- NTP servers (minimum two) are reachable from the management VRF with peer ACLs restricting to internal sources only.
- Config backup repository is reachable with automated backup job and restore test procedure documented.
- Monitoring platform has SNMPv3 or streaming telemetry configured with alert thresholds for CPU, memory, interface errors, and CoPP drops.